Russia says US hacked thousands of iPhones in iOS zero-click attacks

Russian cybersecurity firm Kaspersky says some iPhones on its network were hacked using an iOS vulnerability that installed malware via iMessage zero-click exploits.
The delivery of the message exploits a vulnerability that leads to code execution without requiring any user interaction, leading to the download of additional malicious from the attackers’ server.
Subsequently, the message and attachment are wiped from the device. At the same time, the payload stays behind, running with root privileges to collect system and user information and execute commands sent by the attackers.
Kaspersky says the campaign started in 2019 and reports the attacks are still ongoing. The cybersecurity firm has named the campaign “Operation Triangulation” and is inviting anyone who knows more about it to share information.
Analysis of the malware
As it’s impossible to analyze iOS from the device, Kaspersky used the Mobile Verification Toolkit to create filesystem backups of the infected iPhones to recover information about the attack process and the malware’s function.
While the malware attempts to delete traces of the attack from devices, it still leaves signs of infection, like system file modifications that prevent the installation of iOS updates, abnormal data usage, and the injection of deprecated libraries.
The analysis revealed that the first signs of infection happened in 2019, and the most recent iOS version that was infected by the malicious toolset is 15.7.

Note that the latest major iOS release is 16.5, which might already have fixed the vulnerability used in these malware attacks.
The exploit sent via iMessage triggers an unknown vulnerability in iOS to perform code execution, fetching subsequent stages from the attacker’s server, including privilege escalation exploits.
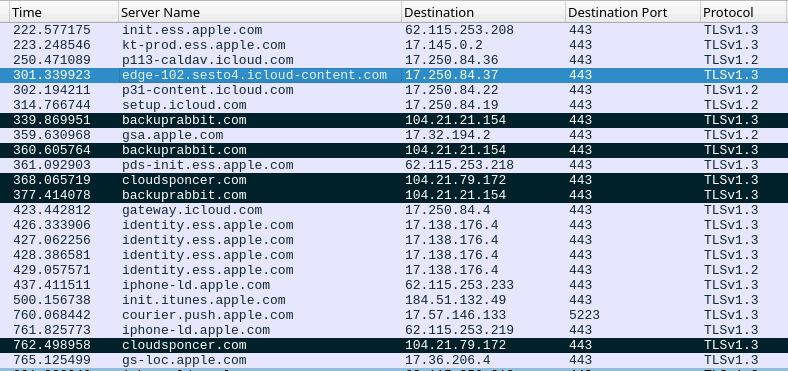
The security firm has provided a list of 15 domains associated with this malicious activity, which security admins can use to check historical DNS logs for possible signs of exploitation on their devices.
After root privilege escalation, the malware downloads a fully-featured toolset that executes commands for collecting system and user information and downloading additional modules from the C2.
Kaspersky notes that the APT toolset dropped on the device has no persistence mechanisms, so a reboot would effectively stop it.
At this time, only a few details about the functions of the malware were made public, as the analysis of the final payload is still underway.
Russia accuses NSA of attacks
In a statement coinciding with Kaspersky’s report, Russia’s FSB intelligence and security agency claims that Apple deliberately provided the NSA with a backdoor it can use to infect iPhones in the country with spyware.
The FSB alleges that it has discovered malware infections on thousands of Apple iPhones belonging to officials within the Russian government and staff from the embassies of Israel, China, and several NATO member nations in Russia.
Despite the seriousness of the allegations, the FSB has provided no proof of its claims.
The Russian state has previously recommended that all presidential administration employees and members switch from using Apple iPhones and, if possible, give up American-made technology entirely.
Kaspersky confirmed to BleepingComputer that the attack impacted its headquarters office in Moscow and employees in other countries. Still, the company stated it’s in no position to verify a link between its finding and FSB’s report, as they do not have the technical details of the government’s investigation.
However, Russia’s CERT released an alert linking FSB’s statement to Kaspersky’s report.
BleepingComputer has contacted Apple to request a comment on both Kaspersky’s findings and FSB’s allegations, but we are still waiting to receive a response.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below


To keep up to date follow us on the below channels.





