The End-User Password Mistakes Putting Your Organization at Risk
Businesses rely on their end-users, but those same users often don’t follow the best security practices. Without the right password security policies, a single end-user password mistake can be a costly breach of your organization’s defenses.
End-users want to do their work quickly and efficiently. Password prompts can be seen as a nuisance, and users may not know the best practices to follow or understand the importance of following them.
Sharing, reusing and weak passwords can put your organization at risk, so having the right policies in place is essential for security!
The Password Risk
Passwords have been a staple of computers for as long as many users can recall and remain essential for securing systems. Though there are many ways to create passwords, not all are equally effective. It is important to consider the various ways a password-protected system can fail.
The most obvious issue is easily-guessed passwords, such as “password1”. An attacker could easily crack this password after only a few attempts. However, passwords can be insecure in other ways, such as reusing the same password across multiple sites, sharing a password with co-workers, or even remembering a password on a public computer.
Easily Hacked Characters and Patterns
Password-cracking technology is ever-evolving and becoming faster. There is even specialized password cracking tools, that are easily attainable. From phishing, to social engineering attacks, brute force attacks, dictionary attacks, and malware – all are forms of password cracking.
Users often use a base word when they build their password. Base words such as password, welcome and admin are widely used and amongst the top ten. When they are prompted to change their password or create a new one, they often substitute numbers for certain letters in a word or add special characters (e.g., “!” or “#”) to the beginning and end of the password.
However, password crackers have incorporated these patterns into their tools, making them less effective.
Password Sharing and Password Reuse
Many users use the same password across multiple sites to make remembering credentials easier. For instance, if a user is scammed on a social media site like Facebook, the attacker could try the same password on the work site.
Altogether, shared passwords and password reuse give attackers multiple ways to target a company through its end-users.
Proper Password Handling Procedures
Password theft and misuse can take many forms. A prime instance is when employees use their personal devices to access company resources and communications. A users personal device may not have the proper security pins in place, leaving them vulnerable.
Also if an employee has their company email on their phone or access to company resources and their device is stolen, without proper security and access controls it creates a huge security risk.
Unfortunately, mobile security is often an afterthought for many organizations.
Best Practices for Securing Passwords
With all the ways passwords can be insecure, what are the best practices for creating and managing them, and how can users be encouraged to follow them? Over time, as organizations have gained more knowledge about password policy, the recommended steps have evolved, particularly in recent years.
- Creating Secure Passwords – Creating a secure password requires more than just avoiding easily hacked characters and passwords. According to NIST recommendations, passwords should be at least eight characters long (if not longer) and not contain sequential characters (e.g., “1234”). Additionally, complexity requirements should be reduced to allow users space to create memorable yet secure passwords.
- Avoid Password Sharing & Password Reuse – A unique password for each site and application, without sharing, ensures that a stolen password elsewhere won’t compromise an organization. Requiring each user to have their account and not allowing shared passwords increases accountability and logging capabilities while enhancing security.
- Verify Passwords aren’t on Breached Password Lists – Before accepting a password creation or change, systems should consult the most up-to-date breached password lists and alert users if the password is deemed insecure.
- Use Multi-Factor Authentication (MFA) – Enhance the security of any password-protected account with Multi-Factor Authentication (MFA). A second factor will limit an attacker’s ability to access the account in the event of a cracked password.
The recent Weak Password Report uncovered that 83% of compromised passwords satisfy the password length and complexity requirements of regulatory password standards. This indicates that even though following best practices, enforcing a strong password policy needs to occur for continuous password security.
Enforcing a Strong Password Policy to Eliminate Vulnerabilities
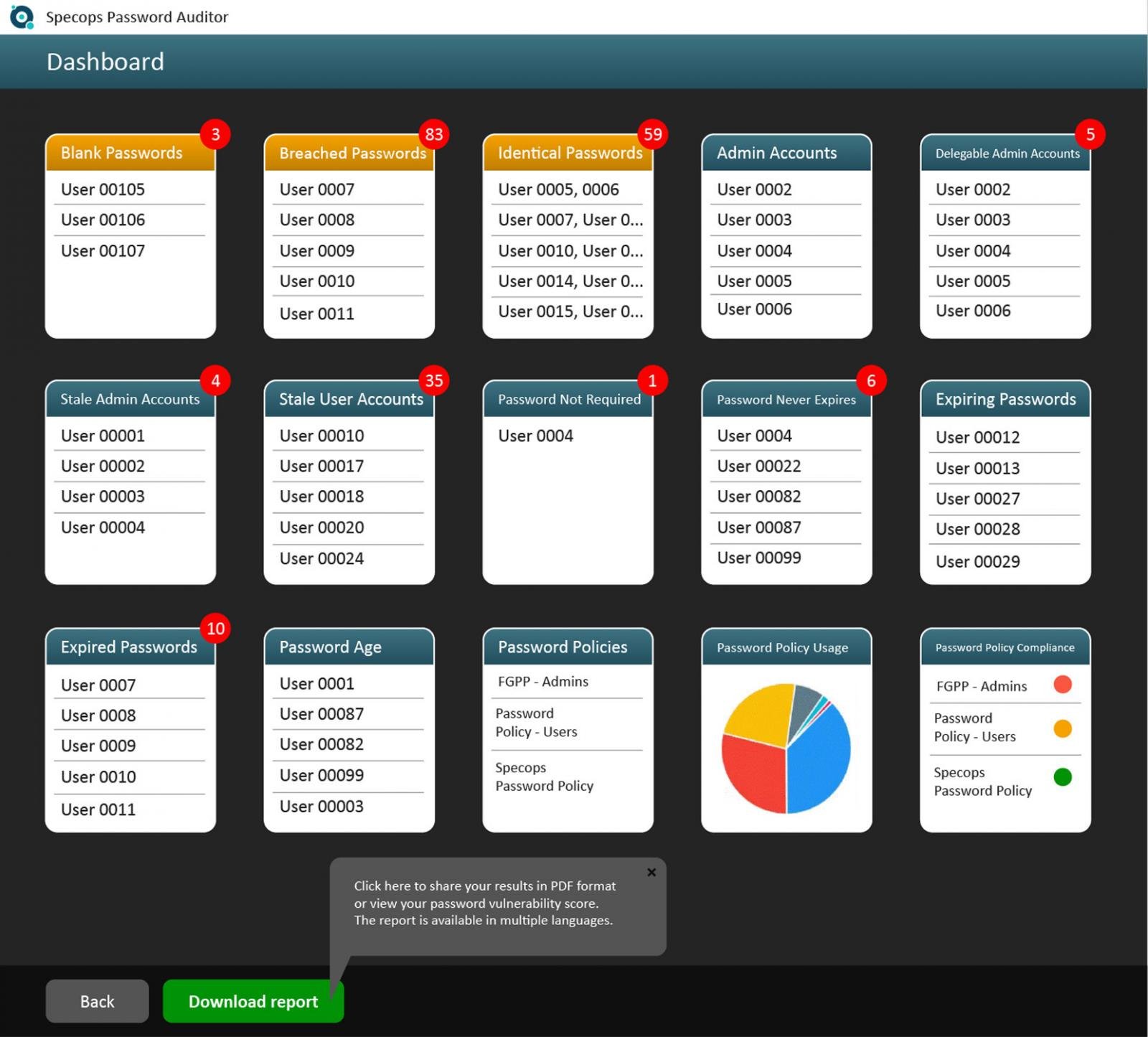
Do you know the general password health of your organization? To do a quick check on the password health of your organization, you can download and run a free scan of your Active Directory.
Perform an in-depth examination of your environment with Specops Password Auditor. Scan your AD for non-compliant passwords or over 940 million passwords compromised and get a free read only report.
This will give you a holistic view of your users and detect password vulnerabilities in your organization.
Despite the emergence of biometrics and passkeys, passwords remain a key component of many business systems. To ensure continued security of your business, it is essential to have a well-defined password policy in place.
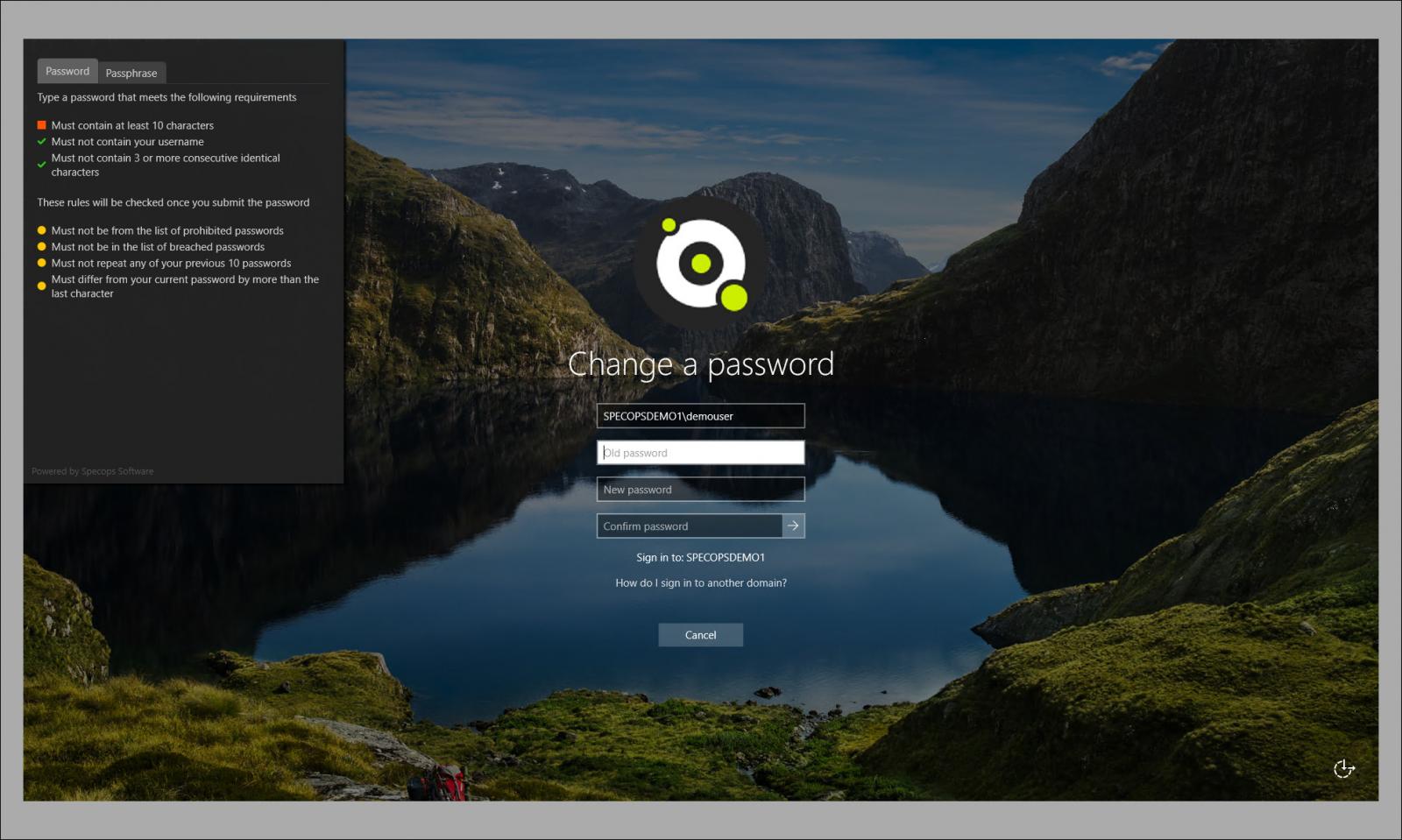
Specops Password Policy boosts the standard Microsoft Active Directory password policies with compliance-oriented templates, comprehensive password creation rules, and breached password protection that allows you to block over 3 billion compromised passwords. With the real-time end user feedback, users can see what is required in password creation as well.
Keeping End-User Passwords Safe
Supporting end-users productivity and safety while maintaining a strong security posture can be challenging. Insecure passwords shared and reused present a very real and persistent threat to any organization.
Secure password policies enforced by tools such as Specops Password Policy keep your environment and end-users secure and reduces vulnerabilities to your organization!
Sponsored and written by Specops Software
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below


To keep up to date follow us on the below channels.





![Cobalt Strike Beacon Detected - 47[.]111[.]117[.]176:443 10 Cobalt-Strike](https://www.redpacketsecurity.com/wp-content/uploads/2021/11/Cobalt-Strike-300x201.jpg)
