Tuta Mail Adds New Quantum Resistant Encryption To Protect Email

Tuta Mail has announced TutaCrypt, a new post-quantum encryption protocol to secure communications from powerful and anticipated decryption attacks.
Tuta Mail is an open-source end-to-end encrypted email service with ten million users. Its creator, Tuta, is based in Germany, where it’s involved in developing post-quantum secure cloud storage and file-sharing solutions for the government.
Today, Tuta announced the launch of TutaCrypt, a new protocol designed to protect currently exchanged communications from ‘harvest now, decrypt later’ attacks.
Harvest now, decrypt later attacks are the act of collecting encrypted data that cannot be currently decrypted to save for the future when more powerful decryption methods become available.
TutaCrypt combines CRYSTALS-Kyber for post-quantum key encapsulation and X25519 for the Elliptic-Curve-Diffie-Hellmann key exchange.
Like others in the field, including Signal and Apple (iMessage), Tuta has opted for a hybrid model approach, combining state-of-the-art quantum-safe algorithms with traditional algorithms to offer complete protection against current and future threats.
The AES 256/Argon2 cryptography remains in place, protecting exchanged messages against current threats.
“With TutaCrypt we are revolutionizing the security of emails. For the first time, people can now send and receive emails that are encrypted so strongly that not even quantum computers will be able to break the encryption and decipher the messages,” stated Tuta’s CEO, Arne Möhle
“And the best thing about Tuta Mail: This unique encryption can be used to send emails end-to-end encrypted to anyone in the world, regardless of their email provider, with a simple password exchange!”
TutaCrypt details
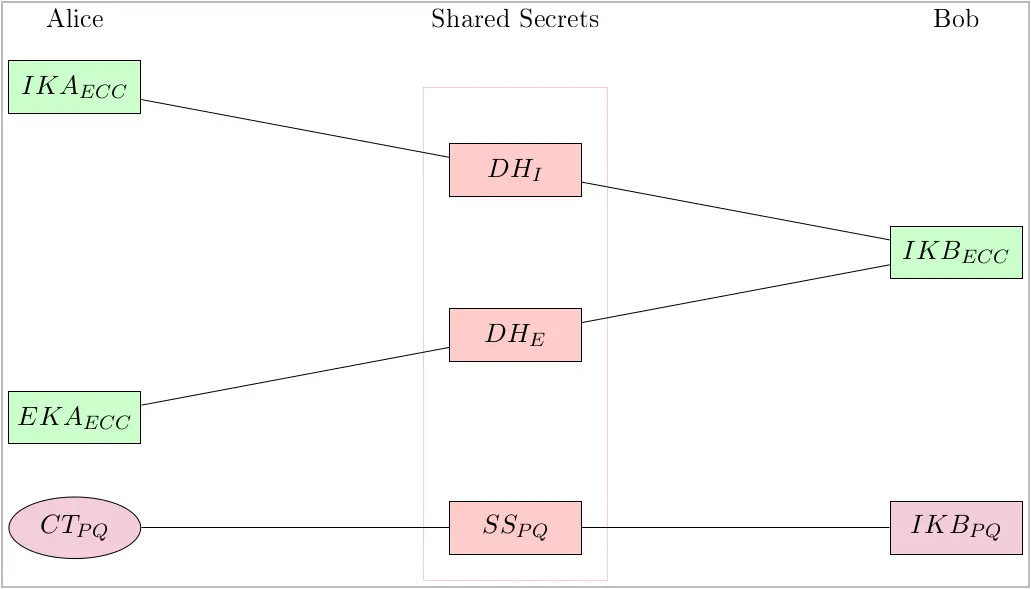
TutaCrypt encryption generates two key pairs for Tuta Mail accounts: an X25519 key pair for the ECDH and a Kyber-1024 key pair for key encapsulation.
These keys, which now replace the old RSA key pairs, are securely stored and encrypted on Tuta’s Germany-based servers and are accessible across user devices.
For authenticated encryption, TutaCrypt employs AES-256 in CBC mode with HMAC-SHA-256.
The protocol derives long-term AES-256 keys to encrypt data stored on the server from the user’s password using Argon2. Symmetric keys are derived using HKDF-SHA-256.
TutaCrypt uses a combination of these algorithms to exchange a cryptographic key, which is then used to encrypt and decrypt the entire message, including its body, subject, and attachments.
The process combines two ECDH-derived shared secrets (DHI and DHE) and a third from Kyber key encapsulation (SSPQ).
These secrets feed into a key derivation function, creating a secure message key for encryption and decryption.
TutaCrypt’s current limitations concern guaranteeing the integrity and authenticity of exchanged messages, as the “classical” algorithms still handle these two aspects. Also, compromise of the long-term identity keys is a risk point.
Cryptographically guaranteed authentication and various improvements in the protocol itself are part of Tuta’s plans.
New Tuta Mail accounts will get TutaCrypt upon creation, and existing users will get the superior protocol through a gradual key rotation that will take place over the next period.
No user action is required when migrating to the new encryption algorithm.
